Is an Alternative Term Used to Describe Asymmetric Cryptographic Algorithms

Asymmetric Cryptography An Overview Sciencedirect Topics


Components Of Asymmetric Block Cipher Download Scientific Diagram

Si110 Asymmetric Public Key Cryptography
Symmetric Vs Asymmetric Encryption 5 Differences Explained By Experts

Ssh Keys Are Simply Known As Secure Shells It Works Like A Cryptographic Protocol Which Is Used For Public Key Cryptography To O Cryptography Key Generate Key

2 Asymmetric Encryption Example Download Scientific Diagram

What Is Altcoin Beliefs Algorithm Cryptocurrency

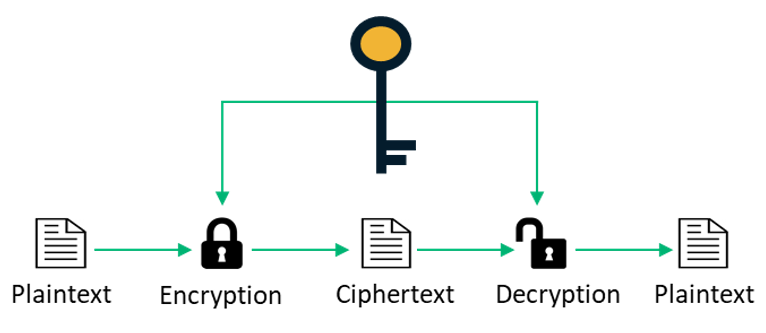
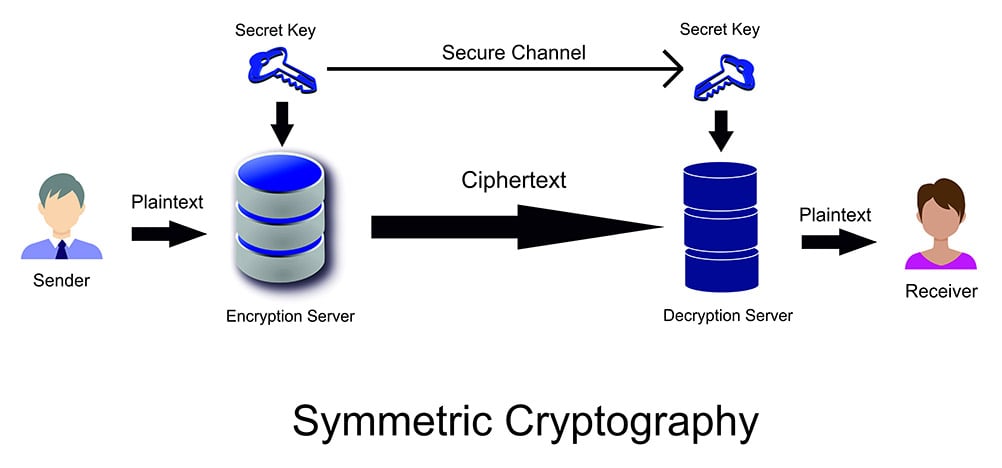
Symmetric Vs Asymmetric Cryptography Cryptography Software Security Symmetric Cryptography

Asymmetric Means You Re Using Two Different Keys One To Encrypt And One To Decrypt We Also Call This Public Safe Internet Cryptography Certificate Authority
Block Diagram Of Symmetric And Asymmetric Key Cryptography Download Scientific Diagram

Asymmetric Cryptography Mastering Blockchain
Asymmetric Cryptography On The Ethereum Blockchain By Colin Sheppard Medium
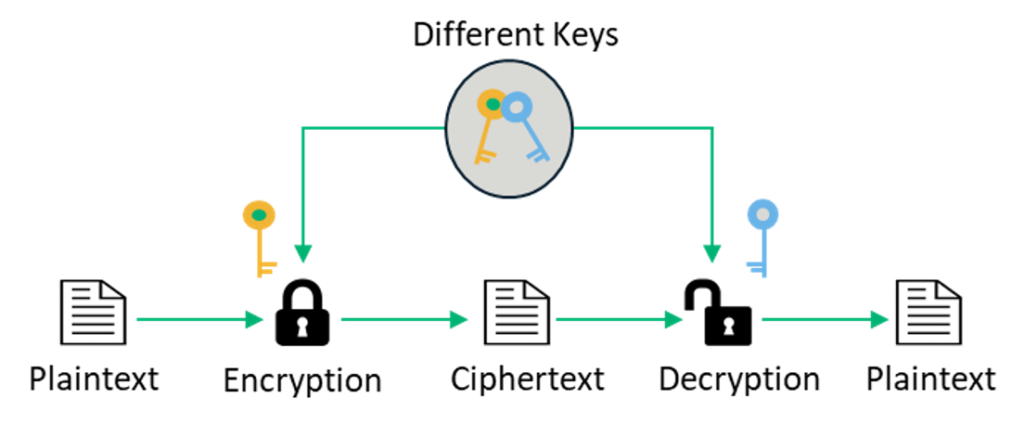
Symmetric Vs Asymmetric Encryption 5 Differences Explained By Experts

Comparative Analysis Between Symmetric And Asymmetric Algorithm Download Table
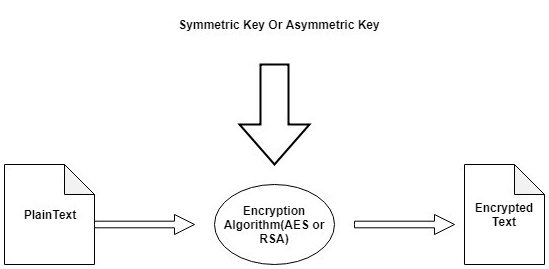
Analysis And Comparison Of Symmetric And Asymmetric Cryptography By Sql Interstellar Medium



Comments
Post a Comment